
High Privilege Admin Accounts and MSSPs
Every organization faces the threat of administrators (and hackers with administrator credentials) using their high privilege accounts to access sensitive
Cord3 protects your most valuable asset – your data. Anywhere. Everywhere. The only Data-Centric Security (DCS) solution built for modern defence operations.
Cord3 Unity redefines information protection, anchoring security directly to the data itself. Our data-centric security architecture establishes a dynamic layer of defence around each individual data object. With DCS, data is self-describing and self-defending — it is encrypted, persistently protected, and bound to security attributes that travel with the data asset. At the point of access, these attributes are evaluated against dynamic organizational policies to enforce releasability, independent of the application or environment. Cord3’s unique On-The-Wire (OTW) enforcement architecture guarantees robust local protection alongside frictionless coalition sharing, natively supporting stringent interoperability standards, such as STANAG 4774/4778 and ACP 240. Crucially, Cord3 Unity decouples security from the underlying IT infrastructure, delivering enterprise-wide data sovereignty without requiring new management layers and ensuring that operational velocity is never compromised.
For over 15 years, Cord3 has focused on the practical application of data-centric security. Working alongside Canadian military R&D, Cord3 developed early foundational technologies, including advanced symmetric key management and security labeling, which enabled DCS to transition into a deployable, defence-grade capability. This mission-critical background informs our approach today and demonstrates our experience in delivering flexible, scalable deployments that protect both structured and unstructured data, enabling secure, policy-driven releasability across complex operational environments.
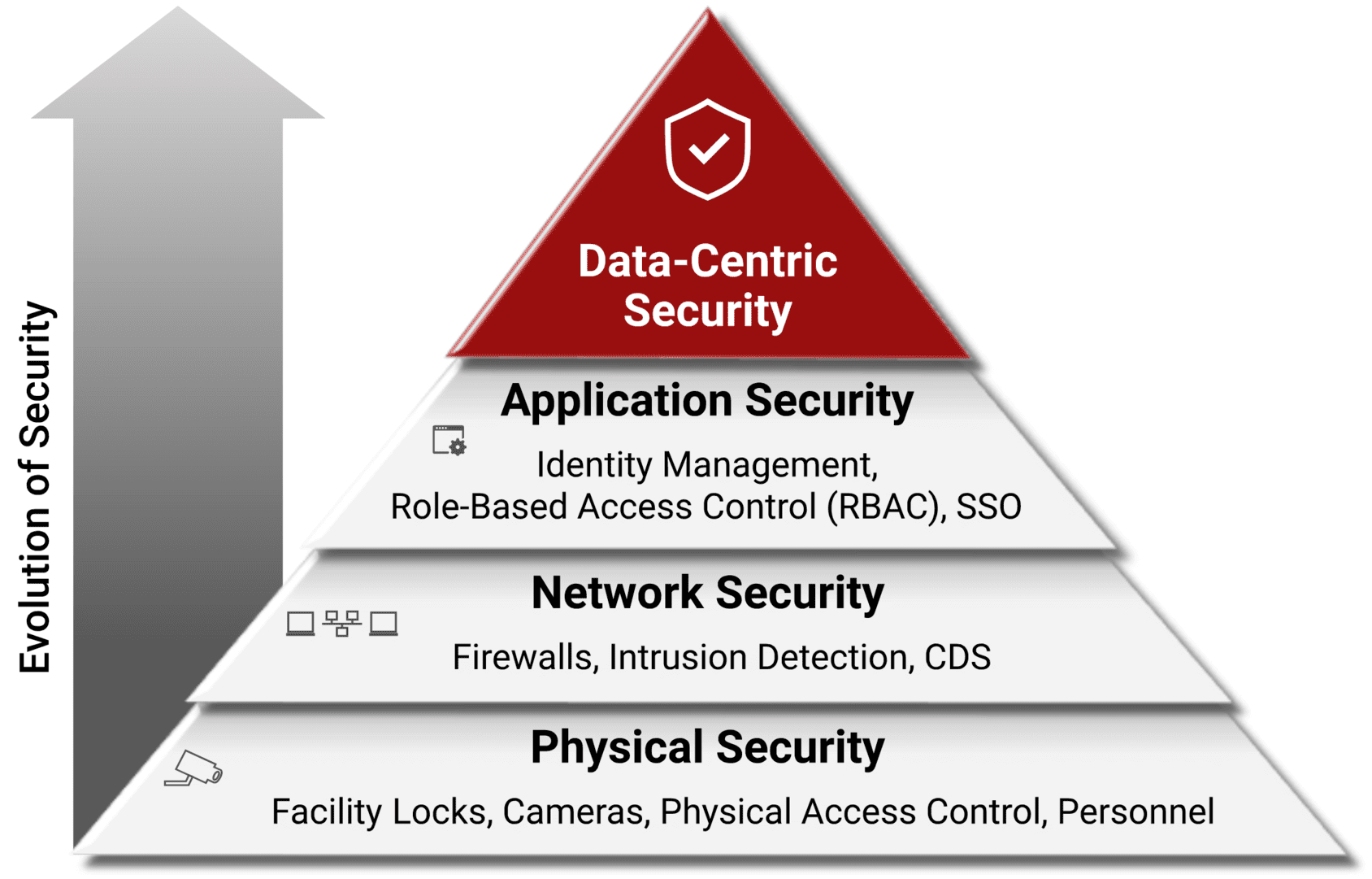
Information Security has traditionally followed the “Fortress” model (strong perimeter / free-flow of data inside) …and yet:


High-level decision making. National command authority and long-term planning.

Campaign management. Theater-wide coordination and resource allocation.

Mission execution at the edge. Real-time engagement and field operations.
Modern warfare requires seamless coordination across every dimension. Cord3 Unity ensures data remains protected as it flows between these distinct yet interconnected domains.
Militaries globally face the critical challenge of operating in an increasingly complex threat environment, where secure data sharing and protection are paramount. With growing cyber threats, coalition data-sharing demands, and the need to safeguard classified information across diverse domains, joint pan domain command and control requires a transformative approach to security. Cord3 offers cutting-edge data-centric security technology supported by Zero Trust. Cord3 DCS protects sensitive data at the element level, enforces access through verified clearances, and ensures seamless interoperability with FVEY and NATO allies, while fully complying with ACP 240 and STANAG 4774/4778 labeling and interoperability standards. By enabling secure, scalable, and real-time decision-making, DCS empowers defence organizations across FVEY and NATO to achieve operational agility, maintain digital sovereignty, and accelerate their Pan Domain Command and Control (PDC2) vision for a data-driven future.

Access to sensitive data is limited to the smallest number of users. People only have access to the information that is essential for them to do their job. By restricting access, organizations can safeguard valuable data, reducing the risk of insider threats and data misuse.
Organizations need to be able to securely share data with both internal and external users. Laws and regulations also require organizations to share certain types of data on demand.
Organizations have a responsibility to provide unsolicited information in response to situational awareness or public safety issues.

Every organization faces the threat of administrators (and hackers with administrator credentials) using their high privilege accounts to access sensitive

It gets worse, not better … There is no denying that the Cloud offers interesting opportunities for organizations to improve

Focus Your Precious Resources on Higher-Value Tasks Are your IT people spending more time than you would like on security



Information Security has traditionally followed the “Fortress” model (strong perimeter / free-flow of data inside) …and yet:Security breaches continue to happen (in 2024 average 4.88M USD / breach) The insider threat is just as serious a threat (30% industry estimate) The need-to-share just as important as need-to-protect All trends point to border-less infrastructures

Cord3 Innovation, a leading provider of DCS solutions, is pleased to announce that it has successfully integrated and demonstrated its

Cord3 is proud to announce that the United States Patent Office has granted Cord3 another patent in the field of
Great news everyone! Cord3 has recently been featured in a book entitled “Safety and Security Science and Technology” as part